TexSAW 2026 - Misc - Three Secrets
Challenge: Misc - Three Secrets
17 solves out of 510 teams; 4th solve by OP_EN.
1. Description and handouts
When the three secrets are brought together only then can the flag be constructed.
Note 1: texsaw{} is already provided to you. Note 2: Please use underscores () between words when submitting your flag. Flag format: texsaw{super_epic_flag} ex: texsaw{orThog0n@l_PiZZ@$0X}
Handouts:
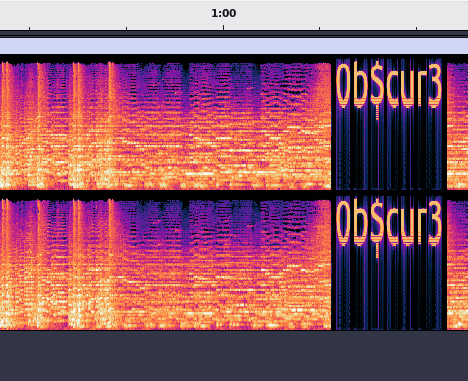
2. Part 1 - one.mp3
Obtaining the first part of the flag is as easy as opening the file in Audacity (or similar) and switching to Spectrogram view:
Part 1 of the flag: Ob$cur3
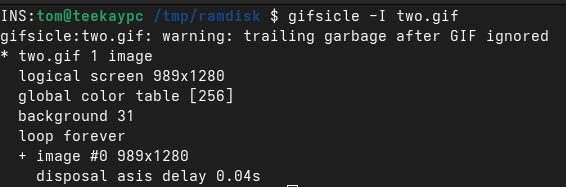
3. Part 2 - two.gif
Opening the file in GIMP or similar reveals that the GIF has only one frame. This is rather odd for a file that weighs 3.4 MB.
Inspecting the file using gifsicle confirms that there is some data appended to it:
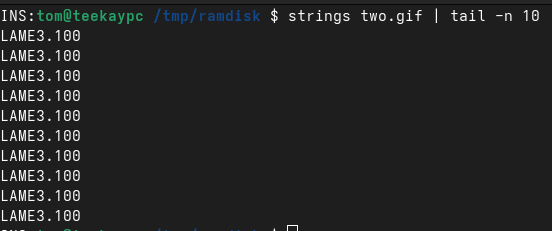
Executing strings on the file indicates that there could be another .mp3 file appended to it, as LAME3.100 is an MP3 encoding library:
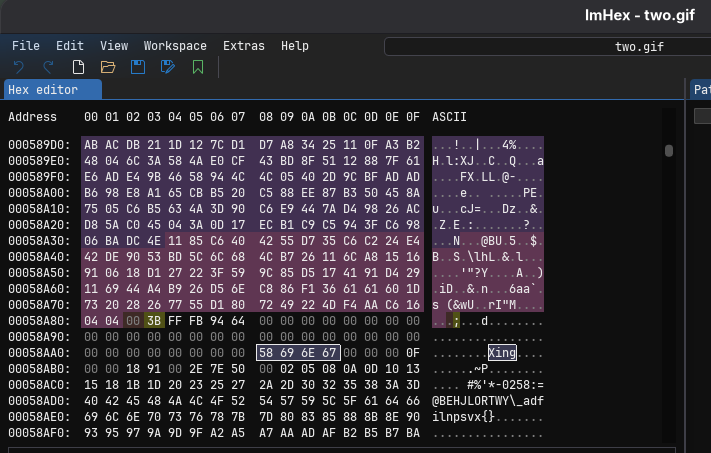
Opening the file in ImHex or similar hex editor, preferably with structure highlighting, shows where the GIF ends and the Xing MP3 header begins:
Executing binwalk on the file does not produce any immediate results. Therefore, extracting the MP3 file can be done by either carving all bytes from the Xing MP3 header to EOF manually, or by using a short script:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
#!/usr/bin/python
gif_file = "two.gif"
output_file = "extracted.mp3"
pattern = bytes([0x58, 0x69, 0x6e, 0x67]) # 58 69 6e 67 "Xing"
with open(gif_file, 'rb') as gif_file:
data = gif_file.read()
offset = data.find(pattern)
mp3_data = data[offset:]
with open(output_file, 'wb') as mp3_file:
mp3_file.write(mp3_data)
Opening the extracted MP3 in Audacity or similar, regardless if in Waveform or Spectrogram view, shows that there’s additional audio appended to the end of the track.
Simply listening to the appended bit in the last few seconds gets us the second part of the flag.
Part 2 of the flag: steganography
4. Part 3 - three.png
After eliminating known steganography methods, I followed the way of researching musical cryptograms. This blogpost points the way to Bücking, Correspondenz systematisch (1804), which was used in this part to simply encrypt the word challenge.
Part 3 of the flag: challenge
5. Flag
1
texsaw{Ob$cur3_steganography_challenge}